這是本文件的舊版!
Support SAM-Account-Name of AD Provider
Introduction
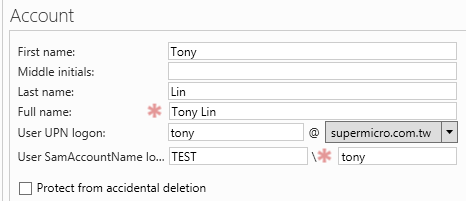
Windows Active Directory提供User Principle Name(簡稱UPN)與SAM Account Name(簡稱SAM)兩種登入方式:
然而ActiveDirectoryLdapAuthenticationProvider僅支援UPN的驗證方式。因此本篇文章主要告訴大家如何支援SAM驗證方式。
How to
ActiveDirectoryLdapAuthenticationProvider驗證UPN的方式,是透過使用者輸入的帳號密碼,並藉由JNDI去做搜尋。而搜尋過濾的條件為:
(&(objectClass=user)(userPrincipalName={0}))所以我們也許可以透過JNDI並搭配搜尋過濾條件去驗證SAM;在開始修改Provider前,我要先確認JNDI是否有辦法支援SAM。我撰寫以下程式碼做確認:
LdapContextSource contextSource = new DefaultSpringSecurityContextSource("ldap://10.134.15.138:389"); contextSource.setBase("DC=TEST,DC=SSM"); //contextSource.setUserDn("test@TEST.SSM"); contextSource.setUserDn("TEST\\test"); contextSource.setPassword("123456"); DirContextAuthenticationStrategy strategy = createTLSStrategy(); contextSource.setAuthenticationStrategy(strategy); contextSource.afterPropertiesSet(); LdapTemplate ldapTemplate = new LdapTemplate(contextSource); ldapTemplate.afterPropertiesSet(); SearchControls sc = new SearchControls(); sc.setSearchScope(SearchControls.SUBTREE_SCOPE); ldapTemplate.search("cn=Users", "(&(objectClass=user)(userPrincipalName=tester@test.ssm))", sc, new NameClassPairCallbackHandler() { @Override public void handleNameClassPair(NameClassPair nameClassPair) { System.out.println(nameClassPair.getName()); } }); ldapTemplate.search("cn=Users", "(&(objectClass=user)(samaccountname=tester))", sc, new NameClassPairCallbackHandler() { @Override public void handleNameClassPair(NameClassPair nameClassPair) { System.out.println(nameClassPair.getName()); } });
Reference
